
The role of IT has strained to continuously evolve. The pandemic has accelerated cloud adoption because of the infrastructure’s dependability and flexibility. A majority of enterprises had to piece together a remote workforce strategy, purchasing ad hoc technology solutions like collaboration tools and cloud-based virtual desktops. A quarter of enterprises purchased a point solution to fill gaps in their existing systems. These strategies have acted as a temporary fix, briefly stemming the flow of challenges, but not enough to be a long-term solution.
Addressing Newfound Challenges
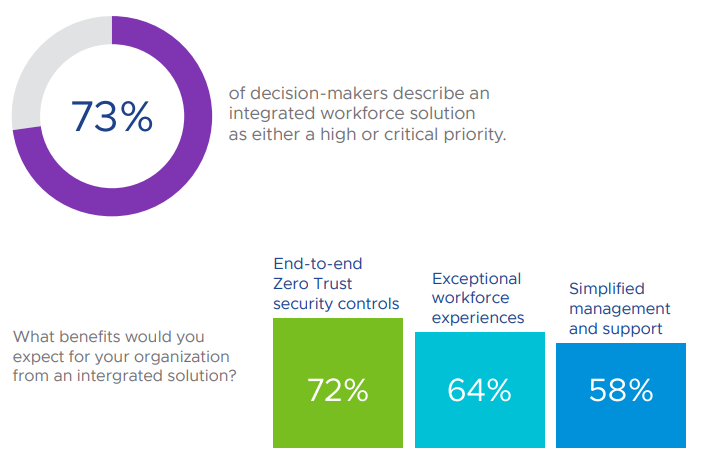
With remote work as the new long-term reality, organizations must move with intention toward a more holistic remote work strategy that balances security, productivity and management. An integrated workforce solution eases pandemic burdens and benefits employees as well as the organization by providing:
- End-to-end Zero Trust security, which moves away from outdated perimeter-based approaches to a model that monitors users, devices, networks, clouds and apps across the network. Zero Trust provides visibility into who accesses data and how they’re accessing it.
- Exceptional technology experiences by bringing seamless access to apps, improved collaboration, and easier training and onboarding directly to employees, anywhere.
- Simplified device management that improves the support experience for IT and enables organizations to better equip employees with devices, apps and connectivity.
Key Recommendations
Implement an integrated solution to fully enable a distributed workforce and promote cross-functional engagement. The solution must provide end-to-end Zero Trust security controls, create exceptional workforce experiences, and simplify the management of devices and networks.
Embrace Zero Trust to secure the remote workforce. To improve the security posture, organizations need to migrate away from VPN point solutions and adopt integrated access solutions based on authentication and authorization prior to network access.
Infuse security throughout the remote workforce access path, including the home environment. A household can have dozens of unknown devices and unauthorized users. Therefore, an employee’s work devices and BYOD platforms must be made as secure as possible with endpoint protection, endpoint detection and response capabilities to let IT protect, detect, and mitigate security issues.
Make employee experience a priority to maintain and recruit a highly engaged and productive workforce. A fully fledged remote work program is no longer a nice-to-have but a strategic advantage. Focus on tailoring and continuously improving employee experience to individual employee needs rather than a one-size-fits-all approach.
Understand the human behind the technology, and identify the challenges that employees face in their daily journeys. Pinpoint which employee experiences are most important to improve, and address specific roles to deliver a more tailored experience, for example, by developing five or six employee personas and then layering in personalization via self-service, BYOD options, qualitative feedback mechanisms, and the use of AI.
Embrace cross-functional cooperation as the role of IT evolves. The shared adversity brought on by the pandemic has helped repair and improve cross-functional relationships. Take this momentum to drive initiatives and foster collaboration across your organization. Focus on use cases that are important to business stakeholders to encourage engagement and buy-in.
